IBM i and the Rise of Ransomware; How to Remediate the Threat
In the past few months it seems every other headline is talking about another industry-disrupting attack performed by various hackers. Whether it’s halting the 5,500-mile oil and gas pipeline for nearly a week or the suspension of meat-packing industry giant JBS people are starting to raise their brow and wonder, what is going on with ransomware? Is it more rampant than usual, or is its trickle-down effect just starting to target more people?
How did ransomware become so common on the IBM i?
For most people, it’s probably surprising how a billion dollar company could fall victim to hackers located halfway across the world. Is the company not investing in their cybersecurity or are the hackers just that good?
Well, both.
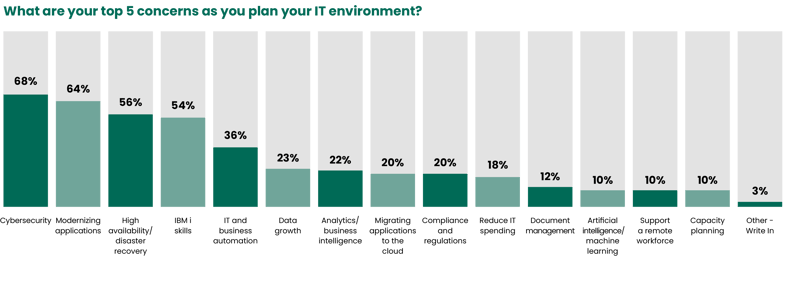
A handful of the companies recently attacked are running the IBM i, a platform whose system admins, according to the charts below provided by the HelpSystems annual survey and report, consider security to be a top concern.
Before moving on, let me clarify one thing. I'm not implying that the IBM i isn’t a safe platform, but rather that, like any platform, steps do need to be taken to keep the IBM i safe and many organizations haven’t taken the appropriate steps.
For many, it’s a general lack of awareness of the importance of security, for others, it’s due to a shortage of financial and time resources which prevent them from staying up to date with the latest security concerns. In a recent interview with IT Jungle, I went into detail as to why security is still a top concern for so many companies and why many struggle to feel confident in their threat remediation plans.
There is work to be done and as cyber attackers become more sophisticated, it’s an arms race to keep ahead of the attacks.
How to Improve Your Threat Remediation
One of our best tips is to take advantage of a CISSP (Certified Information Systems Security Professional) who also has IBM i knowledge on hand. We’re fortunate to have Rob Nettgen  as part of our staff whose infosec knowledge, specifically for the IBM i, is invaluable as he helps guide clients through IT security infrastructure and the best way to set up threat remediation and disaster recovery plans.
as part of our staff whose infosec knowledge, specifically for the IBM i, is invaluable as he helps guide clients through IT security infrastructure and the best way to set up threat remediation and disaster recovery plans.
Rob is often relaying to our clients that cybersecurity is similar to a person’s physical health. Eating healthy is a great place to start, but it alone is likely not enough. You need to also exercise, visit your doctor, and take the necessary precautions to keep your health.
Same with cybersecurity. Information Security is not a one-step solution, it’s a combination of good policies, practices, procedures, security tools and trained professionals making sure the Information Security architecture is in place.
Combatting Ransomware on the IBM i
While many companies are working on tightening their security belts, it may soon become required. With ransomware attacks flooding the recent news cycle, Congress is concerned that if these attacks don’t stop, the country could have a bigger economic problem on hand.
“The next steps that we take… should be a mix of short-term tactical and longer-term national policy shifts," said John Katko, R-N.Y., a member of the House Committee on Homeland Security.
While system infrastructure regulations exist in specific industries (ex. the financial industry, with SEC oversight and mandatory reporting), it may be time for more sectors to have cybersecurity regulations with more oversight and mandatory auditing.
What's Next for Information Security
Irrespective of future regulation, IBM i shops need to take notice and implement information security policies and plans, in addition to their disaster recovery plans. Many companies have been complacent because security was often seemed as a low priority issue on the AS400, but that attitude needs to change. We’re starting to see upticks in clients who contact us saying their competitors just got hit by ransomware and they don’t want to be next.
Now is the time to get ahead of the game.
At Briteskies our approach is holistic, we review your system, identify where the gaps are, and work with you to recommend actions and strategies to help you improve your information security posture.
Yes, there’s a ransomware epidemic going on, but you don’t have to be a victim. You can fight back.
*This article was originally published in 2021 and updated in 2023 to reflect more recent Fortra (formerly HelpSystems) survey results.

